Hi world—Gertie, here. O.G. CISO, and newest member of Veza. I’m also a goat, but don’t let that distract you. I’m not here today to make cheese or eat your laundry, but to tell you why I decided to join Veza.
As CISOs, our jobs are on the line every day. Breaches constantly make headlines, threat actors are getting smarter, and a weak economy is pressuring our budgets. Yet, we’re condemned for incidents that are often out of our control. We’re dependent on employees in other parts of the org chart to do their part for security, and frankly, they don’t always get it right. Even if we do everything by the book, we’re still at risk of being sacrificed when things go wrong. In short, we’re in line to be scapegoats.
If any product or strategy promised to save us, we’ve always been willing to try it. We invested in employee training to prevent phishing, and attackers responded with increasingly sophisticated outreach. We invested in CSPM, but there was always a new zero-day vulnerability to worry about. We invested in MFA, but attackers found gaps, or refocused on compromising personal devices. In short, we were always on the back foot, and the fact that I had two to choose from was no consolation.
But what about least privilege? Least privilege was supposed to save us. Regardless of how an identity might be compromised, we could control the potential damage by making sure identities didn’t hold potentially dangerous privileges they didn’t absolutely need. Least privilege was our chance to be proactive; to get out in front of the next attack, from any vector, and stop it before it could escalate.
The only problem was, as much sense as least privilege makes in principle, most of us are nowhere close to achieving it in the real world. Least privilege, in my world, used to mean relying on individual employees to slow down, carefully evaluate requests, and make complex decisions, while everyone around them demanded that they move faster—“don’t be a blocker.”
Least privilege says: “only the permissions an identity needs to do its work and no more,” but real people don’t know what permissions they’ll need tomorrow, and my identity teams didn’t have time to process multiple requests per person per week, so controlling scope turned out to be harder than it sounded.
We tried centralizing provisioning for all of our apps through an identity platform. Another great idea! But while our IAM team could centralize their own work, we still couldn’t stop various admins throughout the org from creating highly privileged local users (someday I’ll tell you about Gustav the Goat). My visibility to local users was shaky at best, and just between you and me, I got a few warnings from our auditors. Picture a goat in “SOX Jail.” Not a good look.
IGA tools promised to make least privilege easier, but they turned out to have blind spots even the largest of my three brothers could hide in (did you know that goats have a 320 degree field of vision? Not true for IGA tools.) They relied on old-school birthright provisioning, and were rooted in our HR systems, so no help with system accounts or those local admins. At best, they helped us manage membership in groups, without really knowing what permissions those groups conveyed. Did the “Marketing Read Only” group actually confer delete permissions on PCI data? We could only hope not. We needed a modern approach that was rooted in a data-centric view of provisioning. Something that would support “ad-hoc” provisioning when necessary, while allowing us to adopt cloud systems, new SaaS apps, and support teams moving across functions.
In short, with each passing day bringing new identities, groups and roles, plus data systems, SaaS apps, more buckets, more tables with more rows, all adding up to millions of possible individual access decisions, the idea that we could reach and maintain “least privilege” started to seem like a cruel joke. Was this going to be my life? Waiting around for the day an attacker inevitably broke through my perimeter and I was axed to appease the shareholders? Not on my watch! I’ve got kids to feed. Actual kids! I put my hoof down and went looking for a better way.
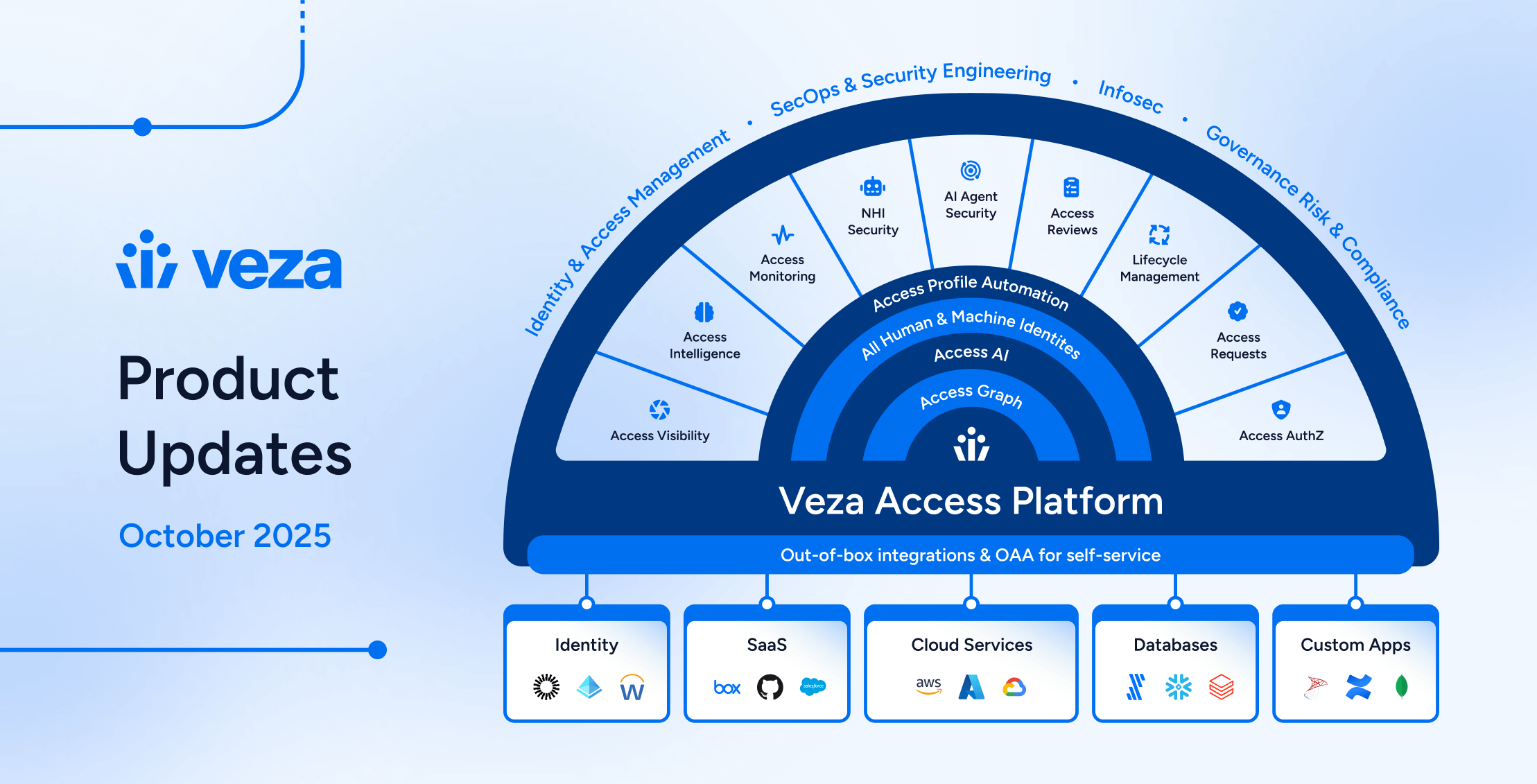
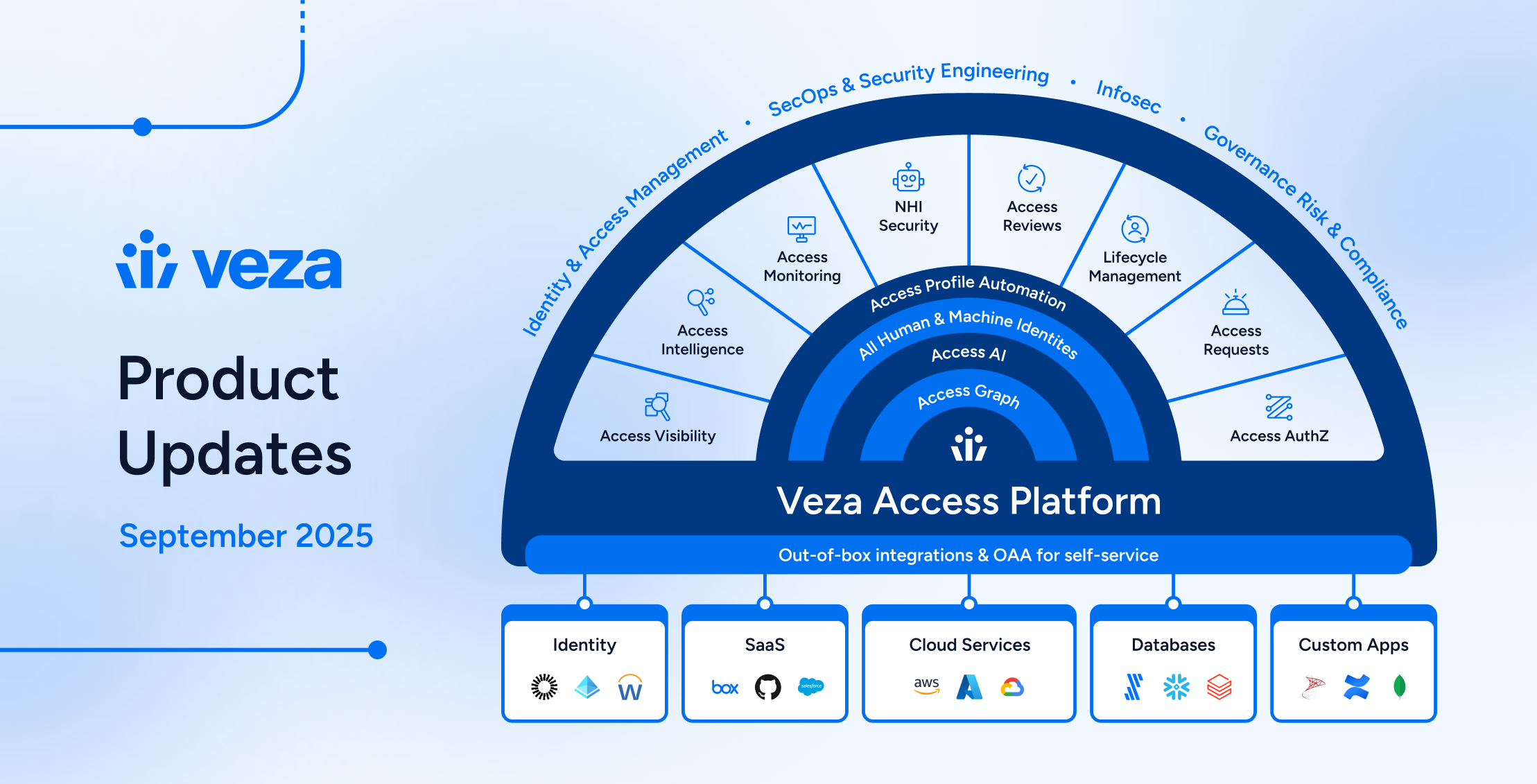
That’s when I found Veza, the first cybersecurity product to give me “security I could see”. With Veza, my company finally had vision as good as mine–no more blindspots. Veza’s identity-first approach to security gave me tools to make meaningful progress on least privilege, automate monitoring for privilege violations, and secure my organization’s data, SaaS apps, and source code.
My story has a happy ending, but many CISOs before me weren’t so lucky. That’s why I’m joining Veza – to take this movement global. I’m committed to a future where every CISO can understand, remediate, and control access at a granular level. A future where being a security professional no longer means waiting to be the scapegoat.
If you’re fed up with waiting to be blamed, you’re in the right place. As my first initiative, I invite all security professionals to join me in the #DontBeAScapegoat movement. I want to empower security professionals everywhere with a new approach to identity-first security and keep them from being needlessly sacrificed when things go wrong. But don’t take my word for it. Schedule a demo to see how Veza can help you.
Sincerely,
Gertie the Goat