The benefits of shifting to cloud are crystal clear, now: According to Price Waterhouse Cooper’s 2022 Pulse Survey, three out of every five C-suite executives named digital transformation their #1 growth driver for 2022. Companies are accelerating the process as much as they dare. But maintaining data security and integrity throughout the transformation is mission critical…and no small challenge for enterprise teams.
Every company’s cloud journey is different, but broadly speaking, migration typically occurs in these four stages.
• First, an enterprise transforms its platform infrastructure into the cloud-based, on-demand architecture of servers and storage, usually through Amazon AWS, Microsoft Azure, or Google GCP.
• Next come the applications, which make it to the cloud on a few different paths. Legacy apps can be swapped out for SaaS equivalents; homegrown apps can be shifted from physical servers to a cloud platform, and so on.
• Third comes the shift to cloud compute, with services like Kubernetes providing an open-source API that manages the complexity of containers deployed across multiple cloud servers.
• And finally, only after all of this is in place, it’s time to move what matters most—your data. Here, it’s solutions like Snowflake that facilitate the transition from on-prem to cloud data storage.
Unfortunately, cloud data has to be protected differently than on-premises resources—you can’t just “lift and shift” legacy data security solutions and processes. Completing your cloud transformation with a smart, strategic, thoughtful transfer of data to the cloud can be a modernizing company’s most pressing challenge, and most of the current solutions are flawed.
Gone are the days when an organization simply places data access control on file systems – securing data across all your tools, on-prem or cloud, for users inside and outside the organization, is the only way to keep data secure at scale. From our experience, Veza is a platform that enables and provides the services we need to secure our digital assets.
Mike Sherwood || Chief Innovation Officer, City of Last Vegas
Cloud Security: New Strategies for a Changed World
Today’s remote or partly remote workers need enterprise access from wherever they are, from any device, and at any time. And this changes the game for security teams. When your workforce isn’t always inside your buildings, or in an easily protectable intranet environment, perimeter-based security measures like keycards and VPNs simply aren’t enough. To thwart today’s sophisticated cyber-attacks without impeding productivity, enterprise teams don’t just need next-generation tools…they need a next-generation mindset.
Welcome to zero trust.
A strict zero-trust security model shifts your line of defense outward, to where it needs to be today. The legacy VPN model made access decisions at a centralized entry point, like a guard at the gate of a castle. For today’s infinitely more complex cloud and multi-cloud ecosystems, zero trust pushes authentication and authorization decisions out to all of the access points across your distributed systems. Individuals attempting to access enterprise resources must authenticate themselves with each access request, and are granted access only when they’re specifically authorized to do so, each and every time. Your cloud data is invisible to threat actors who can’t authenticate, and always accessible to authenticated, authorized parties only, and that usage can be subject to fine-grained controls.
The Growing Necessity for a Data-Centric Approach
Data has become the number one asset for many organizations. When leveraged well, it can be a force multiplier for a competitive enterprise…but its inherent value makes it the principal target for determined threat actors.
And data’s quantity and value are still growing. “The amount of digital data created over the next five years will be greater than twice the amount of data created since the advent of digital storage,” according to International Data Corporation’s 2021 DataSphere and StorageSphere forecast—a powerful testament to the skyrocketing value of data. Today, it’s estimated that up to 90% of a company’s valuation lies in intangible assets like customer information and intellectual property.
Virtually all of the most highly valued businesses in the world today are data companies, including Alibaba, Alphabet, Apple, Amazon, Facebook, Microsoft, and Tencent. And even enterprises that specialize in tangible goods or services require a massive amount of data to compete effectively and make operations run efficiently. Artificial intelligence and machine learning are game-changers, but they require a steady stream of reliable data to outperform their human counterparts, simplify tasks, and save companies millions of dollars every year.
Platforms, storage, and compute are commodities, now: available dynamically on-demand to create, read, update, and delete your data. The transformative value of data is not lost on cyber-criminals, who have structured their approach to extort money from the organizations that value this specific data the most. So how do you safeguard your data from relentless, creative cyberattacks, while safely authorizing your workforce to leverage that data to drive business success?
How Data-Centricity Strengthens A Modern Security Posture
Security that prioritizes data instead of infrastructure lets you protect your enterprise cloud assets while also providing uninterrupted customer experiences and data flow. More specifically, data security tools that sit out of the direct traffic flow can provide real-time analysis and resolution capabilities without compromising data integrity or introducing new challenges to data availability.
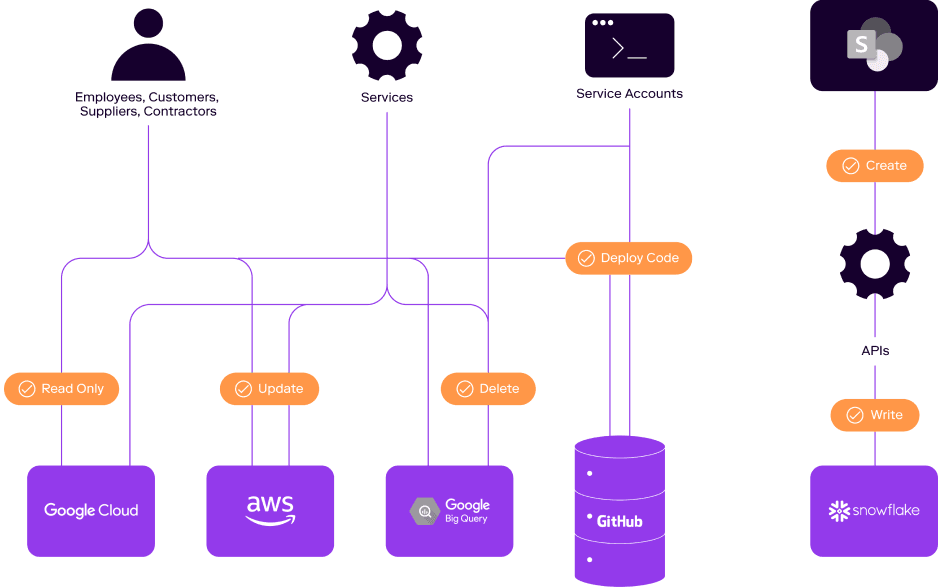
Legacy solutions propose “fixing” data authorization by simply looking at user behavior and removing unused permissions. This is an important exercise, certainly, but over-permissioning is just one risky security practice of many. To provide comprehensive data protection, enterprises need a full picture of authorization across the entire ecosystem. That means clear visibility into every user—including nonhuman service accounts—and the true state of their permissions, including their ability to circumvent the security structure with emergency authorizations (a.k.a. “break-glass” permissions).
Enterprise authorization policies have to be thoroughly examined against best practices as well, because lax permissions rules can open unforeseen security gaps. What happens, in your organization, when a new request for remote access to data comes in before user behavior is available to provide context? When someone requests sensitive data, do you have a system in place to determine whether they’re qualified to handle it—can you see at a glance, for example, if they have existing access to similar types of data, or whether this will be their first time handling it? Can you see what permissions they should have on the data – create, read, update, or delete it?
But perhaps the most important question, for growth-minded organizations, is this: Is your authorization truth consistent and reliable across your entire ecosystem? Automated permissions are critical for scaling cloud environments, but permissions rules for different integrated systems don’t always mesh neatly, leaving IT, security, and compliance teams unsure of their effective permissions—what people are really authorized to do, at any time, with any data, across all integrated systems. Administrators can’t be expected to reinvent the wheel every time a new situation arises, or when an employee has an unusual request or experiences a project shift. Data permissions need to be harmonious across your infrastructure, and coordinated with change management such that new control points can be confidently implemented, with appropriate signoffs, that bypass other processes without creating an IT nightmare or security loophole.
Veza: The Only Security Solution Rooted in the Power of Authorization
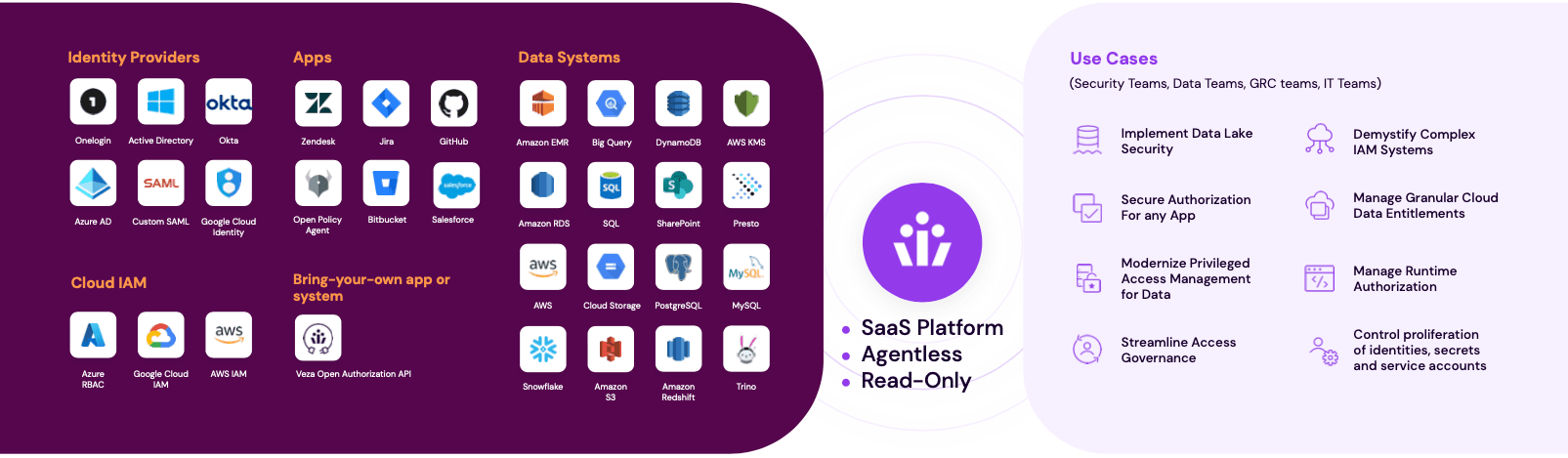
At Veza, we have always understood that strong authorization is the only source of truth to understand who can and should take action on what data. Our data-centric solution features a 360° view into all of an organization’s identity-to-data relationships, mapping identity to apps, cloud permission systems, infrastructure, and data. Only with Veza can you truly understand—and therefore manage—who has access to what data, and exactly what they can do with that access.
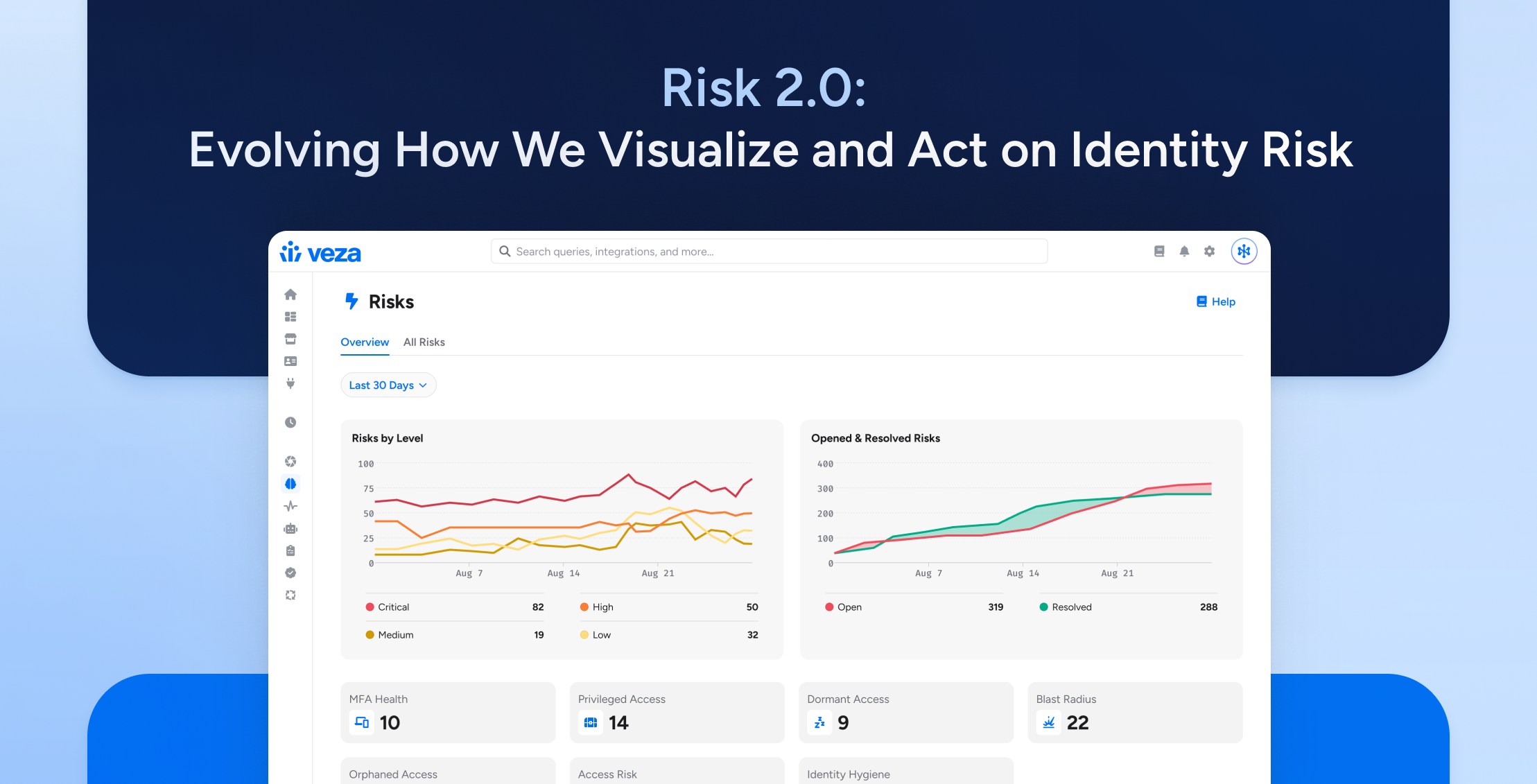
Veza prioritizes protecting your enterprise’s most critical asset: your data. Working out-of-band so data stays continuously available, Veza provides the actionable intelligence your teams need to truly understand and quickly fix your permissions issues. Instead of providing yet another raw data dump for enterprise teams to sift through, our platform presents a clear picture of your true authorization paths, so you can seal any potential security gaps and dramatically reduce the risk of a successful data breach.
Veza adds new insights to your existing change management infrastructure and processes, so you can continue using the systems you already know and trust for enforcing permissions, while gaining fine-tuned control over who has access to what data under what circumstances and exactly what they can do with that access. Our data security platform, built on the power of authorization, brings the comprehensive visibility, deeper insights, smarter controls, and true end to end data protection that today’s cloud-first businesses need.