As fast-growing organizations turn to AWS for their public cloud needs, the challenge in managing the complexity of AWS is expanding quickly and dramatically. According to a 2020 Gartner report, half of all cloud security failures stem from poor management of identities, access, and privilege…and that number is expected to jump to 75% by 2023. Companies that focus on rapid growth without adopting an immediate and sustained focus on managing all cloud identities are putting everything at risk—and the clock is ticking.
Nonhuman identities, for example, are proliferating rapidly in the public cloud, creating a growing security challenge. Access for these identities needs to be governed by the same rules as their human counterparts, including least-privilege and separation of duties mandates. But traditional Identity and Access Management (IAM) solutions don’t often acknowledge or address them at all.
For AWS users, there’s a solution: Adopting strong identity management through AWS IAM.
Quick Refresher: The IAM Basics
The role of Identity and Access Management (IAM) generally is to provide a reliable framework for identifying, understanding, and managing all identities within the system—both human and non-human—so enterprises can intelligently assign access and permissions for each. Strong IAM safeguards identities, protects data, strengthens governance and compliance, and minimizes extra work for IT and security teams.
Different types of security associated with identity include:
- Access Management. This controls which identities—once authenticated—are entitled to use which resources in the cloud.
- Privileged Access Management. This controls access for specific accounts, such as admins, whose elevated privilege makes them favorite targets for identity theft.
- Authorization. This determines a user’s permitted actions on a given resource after the authentication process.
- Governance. This provides centralized control over the entire IAM system, including adding, modifying, and withdrawing specific entitlements to specific resources.
What Does AWS IAM Look Like?
AWS IAM uses this framework to govern AWS resources specifically. A typical AWS environment will include thousands of identities—for humans, devices, organizations, AI entities, and various pieces of code or compute—each of which require permission to access applications, databases and other resources in the cloud. Overpermissioned identities—particularly of the nonhuman kind, where enterprise focus has historically been lacking—can theoretically have access to any part of your AWS cloud infrastructure, adding significant vulnerabilities. That’s why managing these identities is critical.
AWS IAM leverages specific access control concepts to help enterprises determine, at scale, who has what privileges over which resources. These concepts include users, groups, roles, and policies.
- USERS
A user is an entity that you create in AWS—a name plus credentials—to represent a person or application so they can interact with AWS resources and services. Users have permanent long term credentials and a means of authentication. - GROUPS
A group is a collection of users, assembled for the convenience of authorizing multiple related users at the same time—for example, giving all members of the group “Sales Team” access to a new sales kickoff deck in AWS. - ROLES
Roles are entities that interact with AWS in a similar fashion to users, but aren’t tied to individuals. Roles have no long term credentials or passwords—as functions assumed by trusted entities like users or groups, they come with temporary security credentials. - POLICIES
A policy is documentation that specifically outlines which users, groups, and roles can perform which actions on which AWS resources. Policies make user, group, and role definitions meaningful by declaring what each can actually do. (By default, an identity can do nothing within an AWS cloud until permissions are designated.)
Once an enterprise attaches policies to identity entities like users, groups, and roles, defining their permissions, AWS IAM can continually enforce these policies, monitoring and managing access across AWS.
The Multiple Benefits of Modern Identity Management
Monitoring and managing your enterprise identities is critical to modern cloud security and data protection, but that’s just the start. AWS IAM also improves reliability and performance across AWS solutions, and monitoring identities and centralizing access control makes it easier for organizations to remain compliant with regulatory compliance mandates such as HIPAA, PCI DSS, and emerging data privacy laws.
Enterprises can generate audit reports informed with a clear history of enterprise permissions, access and activity, including details like data sensitivity, for example. Role- and group-level permissioning can make it easier to ensure least-privilege access across all an enterprise’s cloud resources, including infrastructure, applications and networks. And if an account is compromised, the record of that compromised identity’s permissions and API activity can quickly clarify what it was theoretically able to access and what it actually DID access over any given timeframe.
Monitoring identities and setting permissions controls centrally also helps reduce risky misconfiguration. Orphaned identities are a prime source of misconfigurations—for example when a permissioned human user leaves the company or changes jobs, or when a non-human identity’s task is over but related permissions aren’t promptly removed. And AWS IAM makes it easier to reduce or eliminate misconfiguration so threat actors never have a chance to take over and leverage an orphaned identity.
How AWS Improves Security Through Identity and Access Management
Across the four types of security associated with identity, here’s how AWS IAM works specifically to enhance cloud security.
- Access Management. Once users are created in AWS IAM, they are provided with credentials for secure authentication, either with AWS single sign-on or multi-factor authentication, or through integration between AWS and IdPs like Okta and Azure AD.
- Privileged Access Management. For highly privileged users, AWS privileged credentials are secured in a PAM vault, providing limited access to the AWS control panel. Best practices dictate that MFA should be required for root access to AWS, and setup session recording and monitoring enabled for root account activity.
- Governance. The centralized access control of the AWS IAM solution lets you easily or automatically modify access for users changing groups or roles, and revoke a departing individual’s access to all applications and services. Teams can monitor how permissions are actually being used over time, and remove any unnecessary permissions in accordance with the principle of least privilege.
- Authorization. Creating identity-based or resource-based policies and attaching these to users, roles, and groups let you intelligently create and modify permissions across a wide range of cloud activity, with AWS IAM enforcing the rules. For example, you can easily allow everyone in Engineers and DevOps groups full access to create, update, and delete EC2 instances, while giving sales read-only access to data in S3 buckets.
Best Practices and Challenges
As with all security systems, following best practices helps ensure the highest level of security for your identities, data, and infrastructure. Here are two critical ones:• Best Practice #1: Apply the Least Privilege principle.
With IAM, perhaps no best practice is more important than providing each human and nonhuman identity with the absolute minimum permissions needed to accomplish their work. This helps minimize the attack surface for breaches, data leaks, lateral attack spread, and other negative outcomes.
• Best Practice #2: Modify policies carefully.
Changing policies too quickly or reactively risks upsetting the delicate balance between security and productivity: either taking away legitimate access from authorized identities (increasing friction), or supplying unnecessary permissions to others (increasing risk).
There’s no question that AWS IAM makes managing cloud-based identities a lot easier, improving cloud security and compliance while relieving enterprise teams of unnecessary busywork. However, there are a few specific challenges that argue for augmenting an AWS IAM system with other solutions.
- Innate complexity. AWS IAM is powerful, but complex—its user guide is nearly 900 pages long. It can be hard to understand what existing policies do, to write policies that do what they’re intended to do, and to safely validate policies (like access controls). And with identities continuing to proliferate (all of which need fine-grained permissioning), the complexity challenge continues to multiply.
- Shifting responsibility. Ultimately, AWS can’t tell customers what access to authorize: The customer needs to define how data should be accessed, and who in their organization can do what. This puts the customer, not AWS, in charge of authoring and maintaining IAM policy, requiring a new set of nontrivial skills your team members may not have been hired for.
- Reality of the multi-cloud. As popular as AWS is, most organizations today have adopted a multi-cloud strategy. As a result, teams need to know how to translate AWS policy to cover instances of Azure, GCP, and other public clouds, maintaining consistency across platforms, policy language, and underlying architectures. It seems unrealistic to expect a siloed cloud-solution provider like AWS to build a first-class solution that supports multi-cloud.
What’s Next (Is AWS IAM Sufficient?)
Increased public cloud deployment brings increased enterprise security risk, and it’s critical for companies leaning into cloud or multi cloud to quickly master modern identity management, including nonhuman identities. Users of AWS already have strong IAM built into their cloud environment, which is potentially a game-changing advantage. Discovering how AWS IAM can help you intelligently understand, secure, and manage all your identities offers the promise of helping you keep access frictionless, and data and other enterprise assets safe.
However, for many enterprises, AWS IAM may not be enough.
Inherent complexity and other limitations can make deploying AWS IAM, and managing it on an ongoing basis, no small challenge. Asking your team to set specific policies across thousands of identities that reliably keep data safe from exposure or exfiltration without hampering enterprise productivity is an almost unthinkably difficult task to tackle in a vacuum. As the primary target of threat actors, your cloud data deserves an extra layer of protection, especially if your organization is growing and scaling quickly.
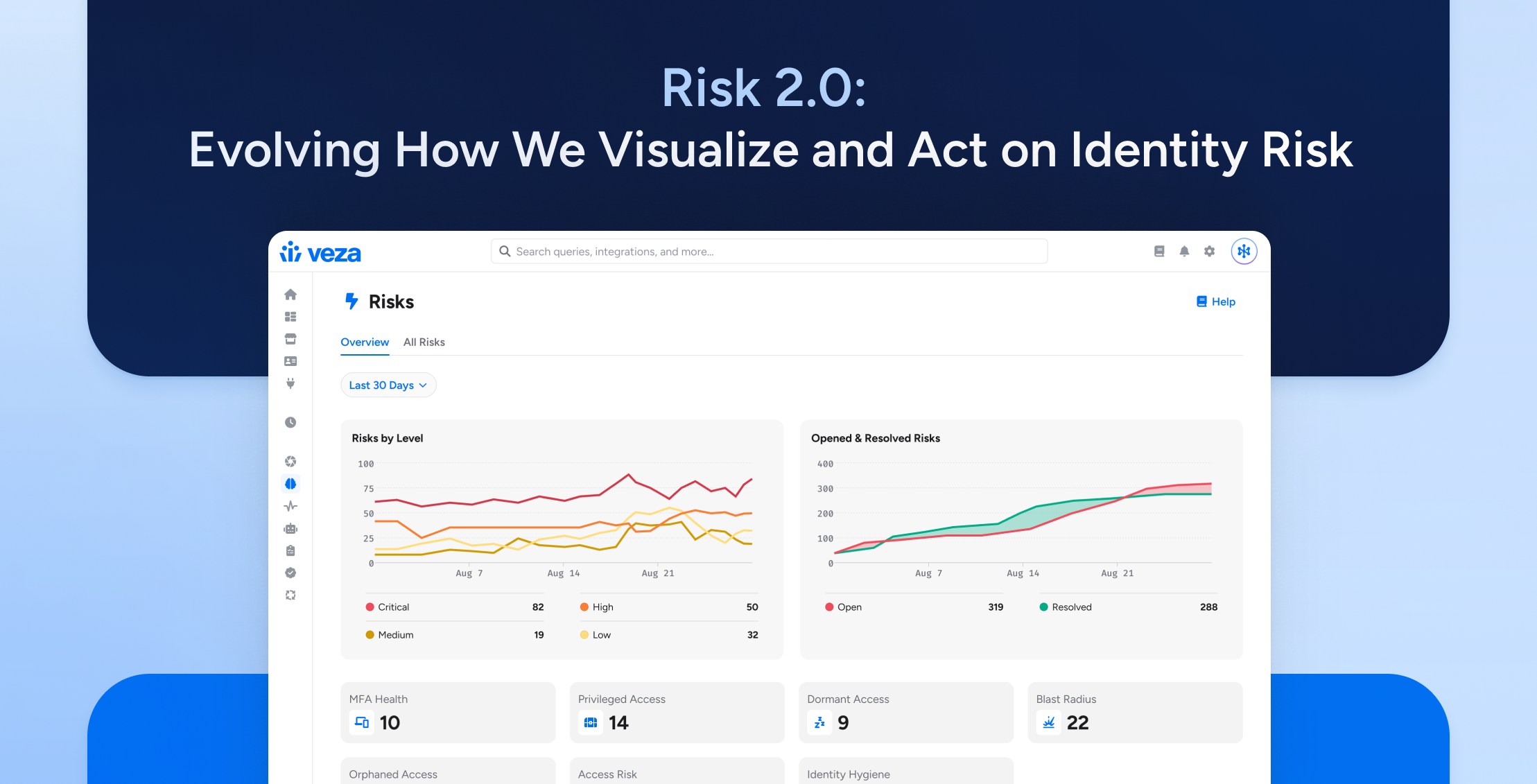
Here’s where Veza can help. Veza adds the dedicated, cloud-first data security you need to protect your organization’s most critical data, while integrating fully and quickly with cloud-native infrastructure permissions systems like AWS IAM. With Veza and AWS IAM working together, you can more easily understand and manage all the identities in your public cloud, attaching the proper policies that permit the safe, frictionless, least-privilege access your teams need while keeping your data safe and your enterprise in compliance.