Over the past two decades I’ve worked with a vast array of organizations to help them defend against the tumultuous threat waters and shifting regulatory tides inherent in the field of cybersecurity and protect what they care about most — their data. While the underlying platforms, infrastructure, and software have shifted over the years, data is still the most valued commodity an organization possesses. Today, the only thing that’s changed is the way it’s transported, stored, and shared.
Digital transformation now pushes data through complex, distributed pipelines where it is enriched, deconstructed into bite-sized chunks, and paired with business logic. From a security perspective, the growing volumes of data and increasingly sophisticated data processing methods have dramatically broadened the attack surface. Flowing from IaaS to PaaS to SaaS — through pipelines and data stores across multiple clouds and on-prem — data traverses a more intricate pathway than ever before. Interwoven across multiple entities and geographies, this increasingly complex ecosystem has added new regulatory dimensions and customer demands regarding how data is handled and who is authorized to interact with it. As a result, it’s become quite difficult for security, privacy, and compliance teams to stay on top of it.
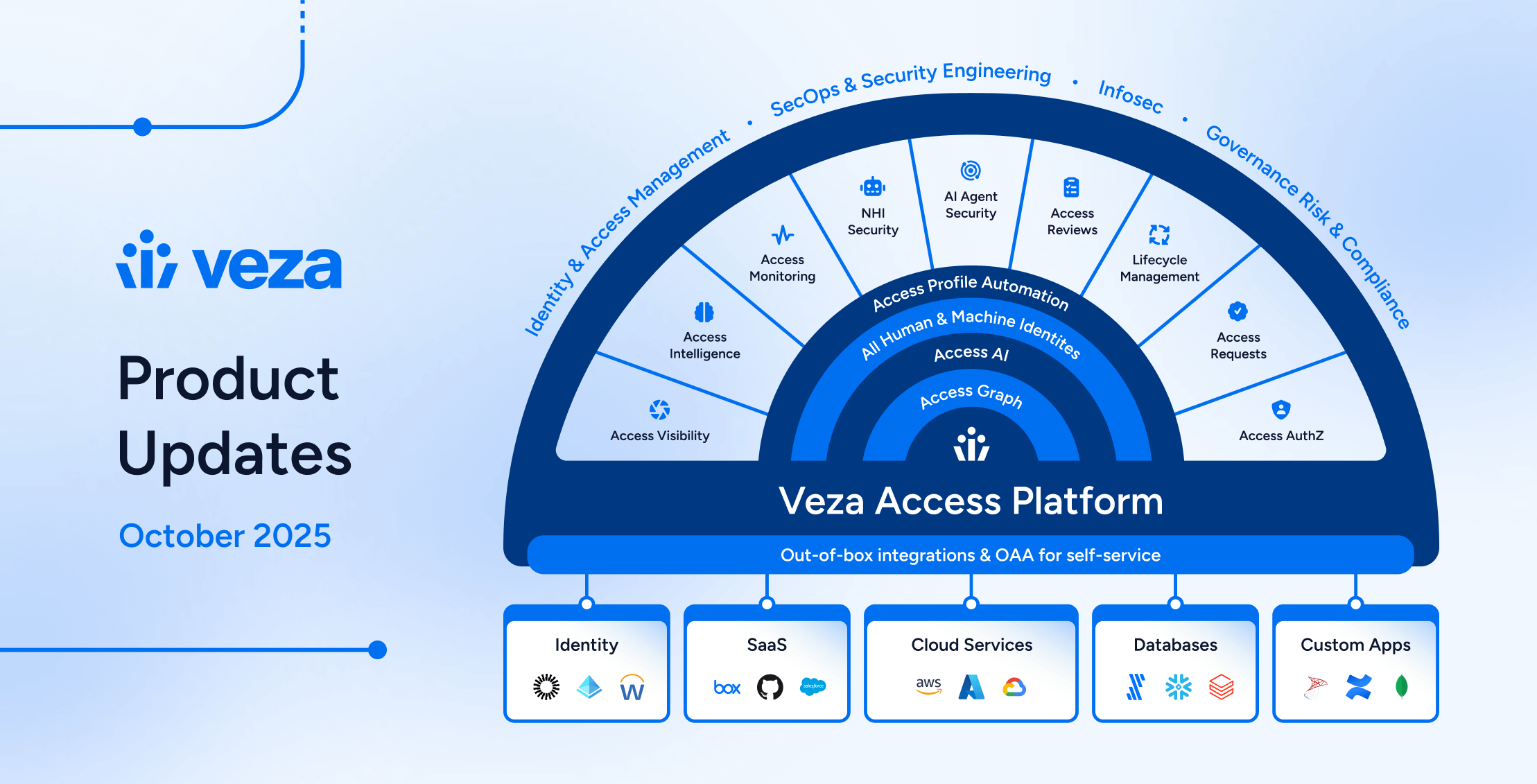
Security teams need to dig deeper. They need visibility, automation, and innovation to break down access control problems and go beyond authentication to manage authorization risks. They need to understand the actions that can be taken on their data — and in what context — and weave it all together to inform effective decision-making. Veza, just recently launched, is enabling security teams to quickly understand and offset these multiplying authorization risks inherent in modern digital architectures.
Shifting the focus to authorization.
Three trends are shaping the way we need to think about data security: First, the cloud is now the de facto standard operating principle for just about everything, in every enterprise. Data is being reconstructed for the cloud and businesses are harnessing its power to deliver great experiences for customers and employees. Next, the definition of “identity” continues to evolve. It’s no longer just internal employees — you now need to manage external user accounts like partners, contractors, and contingent workers as well as non-human accounts like bots, APIs, and service accounts. Lastly, we’re now undergoing the second wave of modern enterprise cloud adoption, which encompasses a hybrid, multi-cloud ecosystem comprised of data systems, apps, infrastructure, and services. Shifting your focus to authorization in this second wave will enable you to truly understand who can take what kind of action on what data.
Why authorization matters.
Organizations have invested a ton in identity as apps, infrastructure, and data have moved to the cloud. But to date, most of those investments have been focused on authentication — in other words, securing logins and verifying the authenticity of the user or account. Authorization takes identity to the next level, securing what a user or account can actually do with their access. That is, what they are allowed to do after being authenticated. This is critical and it’s not easy to get right with the authorization complexity that exists under the tip of the authentication iceberg. More often than not, organizations unknowingly fall victim to overly entitled access and then find out by looking — and learning — through the data breach rearview mirror after it’s too late. And since data typically holds sensitive details like customer information, PII, PHI, company IP, trade secrets, and more, securing authorization for data access is essential for protecting your company and enabling it to meet its compliance requirements.
Veza: A powerhouse data-security platform rooted in authorization.
There are plenty of cybersecurity tools out there. I like how Veza is aggressively attacking the complexity of the authorization problem and can tell you not just who and what has access to what, but what actions can and should be enacted on your data. Veza provides more than just visibility to help you enforce the principle of least privilege. The platform truly enables organizations to see every type of enterprise identity and its associated level of access and permissions to any enterprise resource, down to the data level. With Veza you can verify who should have access to just the right resources they need to do their job. And once they’ve been authorized, you can set up controls over what users and accounts can do with those resources — create, read, update or delete. Veza also facilitates access reviews and entitlement audits, enables real-time alerting on policy violations, and provides guidance on remediating over-permissioned users, which is especially important for organizations facing an ever-growing set of regulatory compliance demands.
The time is now.
As security professionals we must unpack and deal with the authorization complexity and risks in front of us. We are in an evolving era of explosive data growth paired with increasingly sophisticated methods of data processing. The sheer quantity and variety of paths to your data are far greater and more complex today. The number of fine-grained entitlements required to enable this ecosystem to thrive are the same ones that are challenging both our security and compliance assumptions. We need to act now. Veza’s mission to become the industry’s most trusted platform for data security in the cloud is already two years in the making. I’m very excited to leverage what they have already learned and to see what’s next.
If your organization is in the midst of accelerating data adoption in the cloud, building authoritative access controls, taking a zero trust approach to data security or just interested in learning how to rethink data security for the second wave of enterprise cloud, check out Veza today.