The pandemic gave companies a swift kick in the butt to get a move on digital transformation and cloud migration. With remote work here to stay and increasingly stringent compliance laws, how we work continues to be transformed.
Talking with Identiverse attendees last week, we asked: In what way has your organization’s cloud adoption accelerated in the past 5 years? The top 2 answers?
- We are migrating data to the cloud including data lake/warehouse adoption)
- We have adopted a multi-cloud approach (infrastructure, apps, data systems, etc)
In fact, the Identiverse 2022 conference was a chance to take a moment to connect, reflect, and reassess what’s working (and what’s not) in security and identity after a rapid move to the cloud during the pandemic.

At the Veza booth, we spoke with attendees*, gaining first-hand information about how they are adapting to cloud migration. Looking at the information as a whole, we learned that businesses are well on their way to adopting cloud-native data solutions. And, while audits happen regularly, we’re still hearing news of data breaches in the headlines every day, which means….there must be something missing.
Here’s something many didn’t consider: as cloud adoption increased, so did the varieties of identities to manage. While yesterday was all about on-prem, with some cloud access for employees, today there is a combination of on-prem and cloud app access for employees, contractors, partners, as well as non-human identities like service accounts and bots, and even APIs. Without a strong identity foundation, maintaining access control for a rapidly growing number of identities is impossible.
As expected, many organizations implement the more basic concepts of identity associated with authentication
- authentication capabilities through single sign-on (SSO);
- multi-factor authentication (MFA); and
- cloud-based user directories
But security protection is only good if you use it. In an interesting interview during the event with SC Media, Julie Smith, Identity Defined Security Alliance executive director, shared that their most recent report less than 50% of companies actually implement MFA. Essentially, many companies were offering MFA, but few were enforcing it. This could be a big reason that:
- 79% of companies experienced an identity related breach in 2020
- 84% of companies experienced an identity related breach in 2021
Because if there’s one thing Identiverse attendees can agree on, it’s that identity is the foundation to a security program – and the starting point for a Zero Trust implementation.
At the event, you didn’t need to look further than the captivating keynote on the first day to see how a hacker could bypass identity verification protocols. :
- Hacking Trust: Bypassing Identity Verification Protocols with Social Engineering (and How To Stop Me), Speaker: Rachel Tobac
As one attendee tweeted, “The way Rachel Tobac highlighted the customer support channel as the pre-eminent attack vector makes the Arynn Crow’s session, Identity on the Front Line: IAM for Customer Service, a must see.”
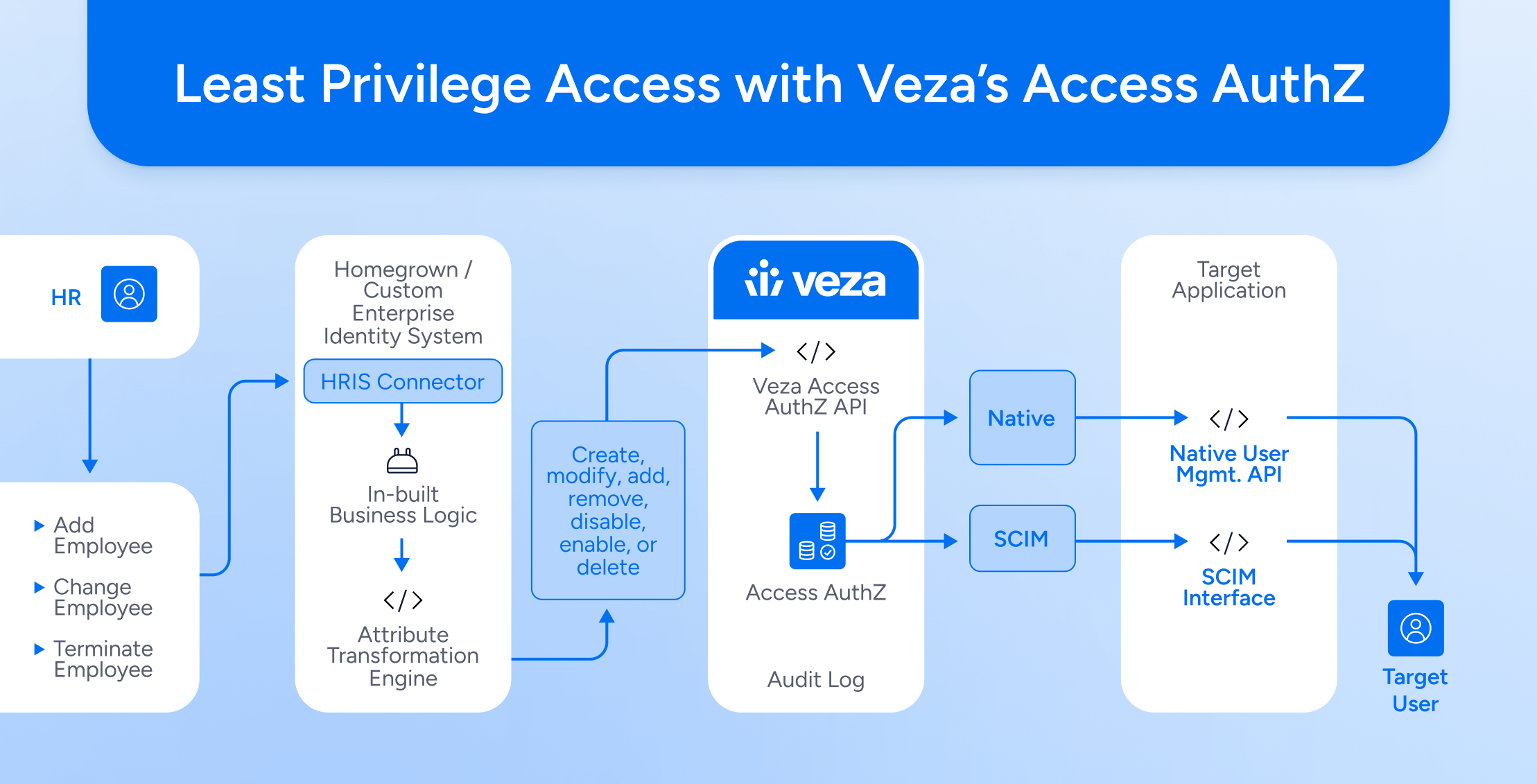
This begs the question – even if companies are using identity verification protocols (many are not), if an account is hacked, what happens after access is initiated? What data is exposed once a privilege account is accessed? What combination of authorization permissions makes a hack even more severe? This is where it’s so important to understand and manage authorization (what you can do with the access you have) across all cloud services – apps, data systems, and more.
When we asked attendees how regularly their company reviewed, updated & audited identity permissions to cloud data systems, the top 3 answers (in order) were:
- Quarterly
- Weekly
- Monthly
Audits are great, but when data breaches are still so common in headlines, something must be missing in those audits. So – what does this tell us? Ultimately, companies can do a better job with security – continuously monitoring and tweaking solutions that already exist. But it’s also time to think about security in terms of data – and taking the next step to managing authorization in multi-cloud environments.
Here’s where Veza can help – we bring a new perspective to security that focuses on what matters the most – data. Using Veza, organizations benefit from achieving business use cases tied to privileged access for data, management of data access control, facilitating cloud entitlements, and much more!
Identiverse is one of the top identity conferences of the year. Here’s some other security events coming up in 2022 –
Be sure to catch Veza at Black Hat and Gartner IAM next month!
- Xchange Security – July 11
- FutureCon St. Louis – July 13
- Black Hat 2022 – Aug 6
- (for you Identity enthusiasts) – Gartner IAM – August 22
- Blue Team Con – Aug 27
- Cybersecurity Expo – Sep 14
- SECtember 2022 – Sep 26
- InfoSec World – Sep 26
- IDM Europe – Oct 4
- ISC2 Security Congress – Oct 10
*If you want to see how your answers might fare against Identiverse attendees, drop us an email and we’ll send over a summary of the results.