One of today’s fastest-growing cybercrimes, ransomware has seen a 700% YoY growth rate (2020-21) becoming a $20B a year industry. Ransomware is a destructive class of malware that encrypts an organization’s data rendering it unreadable. Launched primarily via phishing emails aimed at stealing user credentials to infiltrate corporate networks, the financially motivated attacks hold data for ransom, promising to decrypt it once a payoff is made. The costs incurred to remediate, and restore business operations can be significant. In an international business survey, 46% of companies reported that some or all of their data was corrupted during recovery, indicating that irreparable damage was done regardless of a payment being made.
Attacks typically unfold in three stages:
Delivery – To get started, the payload needs to be inserted into a target machine. Delivery methods include spam and phishing emails containing links to malicious sites where user credentials can be lifted and the exploitation of vulnerabilities in internet-exposed services and remote access services like VPNs and Remote Desktop Protocol (RDP). Lack of cybersecurity awareness on the part of end-users and weak passwords also serve as attack enablers.
Execution – Here, the payload starts running on a workstation or server, quickly encrypting data files.
Propagation – Once things get going, the ransomware gets copied to as many machines as possible, generally via malicious authentication with compromised credentials. A common, highly vulnerable attack surface is shared folders as enterprise users typically have access to many.
Current methods of prevention
Protection against ransomware requires multiple layers of defense. A few solutions organizations have used to defend against ransomware are
- Email security gateways to detect and remove risky content
- Endpoint protection to terminate the execution of processes detected as ransomware
- Multifactor authentication to deter attackers from harvesting compromised credentials
- Data loss prevention software to detect potential data breaches and exfiltration
Security tools that focus on access and authentication aren’t enough
Access and authentication controls aren’t sufficient to prevent the automated propagation of a ransomware payload, often used in ransomware attacks, because an attacker needs to be able to write over the data with encryption, which generally is only allowed to a small set of privileged accounts. Privilege abuse is essential for a ransomware attack to be successful. To control privilege abuse organizations need to be able to see and control who has permissions to encrypt the data, not just read it.
Veza’s solution: The authorization platform for data
Many legacy security tools were not designed to secure data in cloud-native data systems. While enterprises might have tools for data classification, data loss prevention, access and entitlement governance, and privilege access, organizations still struggled to confidently answer “who can and should take what action on what data.” That is the core question that needs to be answered in order to secure enterprise data.
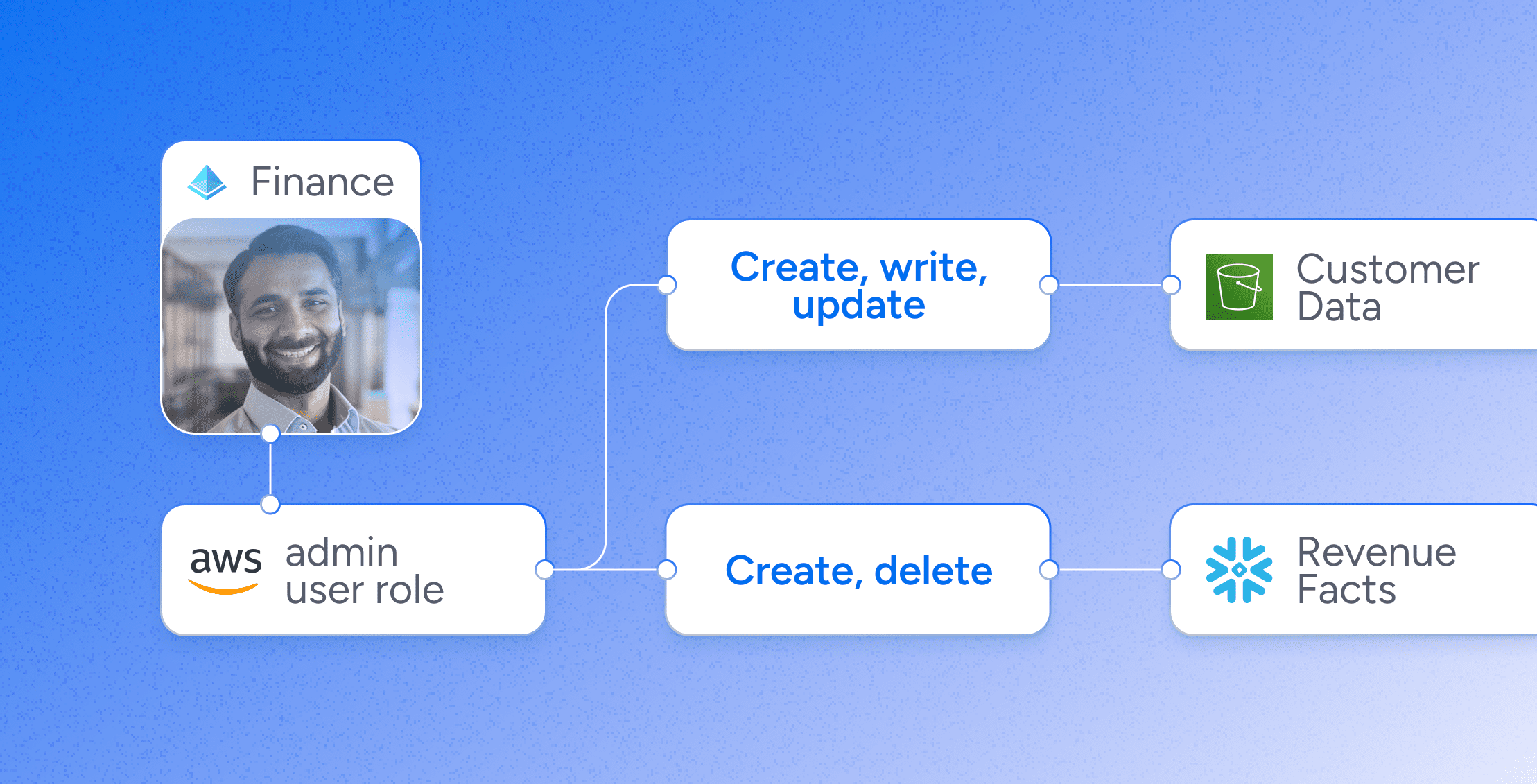
Veza enables organizations to understand and control the scope of privileged access in their organization, identifying high-risk attack vectors that could be exploited by ransomware threat actors. By bringing visibility into data permissions, Veza helps organizations understand and reduce their exposure to ransomware risk. For example, Veza identifies elevated permissions and areas of risk such as identifying:
- Human and service accounts with administrative privileges in GitHub
- Okta users that have access to delete sensitive data in BigQuery
- Undersecured data stores such as S3 buckets with no access logging
To protect against ransomware attacks, the Veza solution enables organizations to gain full visibility across all identity-to-data relationships to understand the scope of the attack surface. By enabling you to understand and control who has high-risk permissions that may include data encryption privileges, Veza gives you the power to prevent privilege abuse to deny bad actors authorization to access data and avoid paying the ransom. To learn more about how Veza can help your organization use the power of authorization to secure your data and mitigate your risk of a successful ransomware attack, schedule a demo today.