Authorization: The Missing Piece of Cloud Security
Authorization—the ability for enterprises to make informed, centralized decisions at scale about who should take action on what enterprise resources—is a growing challenge. Keeping enterprise data secure has always been a mission-critical function for every organization. But as we shift toward modern, complex, multi-cloud ecosystems accessed by varying identities, it grows harder to secure enterprise data while keeping it accessible for authorized parties. Today’s security teams need new tools to optimize data security—and that starts with a thorough understanding of the many dimensions of modern authorization principles.
Fundamentally, authorization is about making sure the right people have the right access to and can take action on the right resources at the right time. A company needs to give its workers frictionless access to the enterprise assets and tools they need to stay productive, while protecting those assets and tools from threat actors, whose favorite tactic is posing as legitimate employees. A local diner with seven employees requesting access to the walk-in freezer or the cash register? No problem. But for a global enterprise with thousands of employees, contractors, partners, and machine identities accessing and sharing cloud-based assets all over the world, the challenge is sobering. You might, for example, be tempted to give your beloved CEO the right to access anything she wants. But what happens when a disgruntled former employee hacks her identity or steals her keycard?
Making data accessible to authorized parties without compromising security isn’t easy, and the bigger and the more complex an organization gets, the harder it is to safely automate authorization at scale. Strong security without easy accessibility adds friction, cost, and inefficiency to business operations. Easy accessibility without strong security leads to compliance nightmares and data breaches. You need a solution that accomplishes both.
First Principle: Authorization vs. Authentication
Authorization is sometimes confused with authentication, which is the validation of an identity. Authentication proves an identity is who they say they are—once that’s established, authorization provides that authenticated identity with specific permissions to access, share, or otherwise interact with specific enterprise resources. When a visitor to your building presents their driver’s licence at the door to prove they’re John Smith, that’s authentication. When your doorman hands this authenticated John Smith a pass to get through the security gates, that’s authorization. As a guest, John Smith might be narrowly permissioned to use only the elevator that goes to your floor, not the building owner’s penthouse, and they likely won’t have rights to grant others entry into the building, and so on.
With digital cloud access, each identity in the ecosystem is assigned a credential – a password or a biometric, for example—to authenticate itself whenever it needs to access a network, application or database. An authenticated identity is granted certain permissions, sometimes based on role, status, geography, and other factors. For example, everyone whose department is Sales might be authorized to use the Salesforce application, but only sales managers might be authorized to see a database that includes sales team compensation, and only the Chief Revenue Officer might be authorized to share or change that compensation database.
The purpose of authorization is to give identities access to the resources they need to perform a necessary function—and no more. Best practices include the principle of least privilege, which ensures that nobody has permissions they don’t actually need, because these represent unwarranted security risks. Smart permissions management lets you automate some authorization functions to unburden IT and decrease risk (for example, ensuring that a person who transfers out of a department instantly and automatically loses access to databases relevant only to that department). Authorization has historically received less attention than authentication, but its importance is growing quickly in a multi-cloud world.
Why Organizations Should Shift their Focus to Authorization
Having the right tools and systems in place to centrally control data access permissions is critical. Weak or improper authorization procedures can quickly lead to compliance violations, the leaking of personally identifiable information, ransomware attacks, data breaches, and other disastrous outcomes. Some specific driving factors behind the rise of strong authorization:
- Strong authorization limits damage from cyberattacks like ransomware and privilege abuse. If a threat actor somehow gains access to the network, tight access permissioning will limit their ability to move laterally and compromise other parts of the network.
- Governments and other regulatory agencies are tightening data privacy laws and compliance mandates. Companies need to understand and manage enterprise access and its governance at a finer level of detail than ever. Falling out of compliance can expose a company to heavy fines or lawsuits.
- Strong authorization helps build and preserve consumer trust. Reputation matters: To maintain long-term consumer trust, companies must demonstrate they can protect sensitive data, guard against leaks, and share information responsibly.
- Zero Trust security requires centralized, fine-grained authorization. As more organizations adopt the Zero Trust security model, they need to be able to carefully define and safely automate access permissions for authenticated identities, freeing IT and security teams for other work.
Why Organizations Must Master Authorization
Data is an organization’s most valuable asset, which is why it’s a prime target for threat actors. But the wrong approach to data security can reduce efficiency (by adding unnecessary access friction), or put enterprise assets at risk (by over-permissioning parties with access they don’t need, and that threat actors can exploit).
Role- and group-based authorization helps enterprises balance this need by supplying permissions that are a function of the task at hand, the project’s organizational structure, and the project’s timeframe. This helps minimize over permissioning, for example by having permissions that are only valid for the timespan of the active project. Even non-human identities like ad hoc service accounts and bots also touch data, so must be addressed. Once a task is completed, an identity may no longer bother to access an application—but if they remain authorized to do so, these “orphaned” identities can be unwitting targets for data breaches.
Strong authorization can be fine-tuned to supply least privilege access to different groups and resources without restraining productivity. For example, actions available to a user on one set of relevant infrastructure resources may not necessarily be provided across a less relevant set of servers and networks. Access to data can be restricted based on the sensitivity or data type, or based on specific roles within a project group. Some users might be allowed to read, write and create data, while others may have read-only permissions.
Finding the Right Authorization Tools
To harden your data security through strong, centralized, fine-grained access permissions, look for authorization solutions with these characteristics:
- Cloud-native scalability that can meet the expanding needs of a growing, data-rich business, no matter whether the data is stored on-premise, in a multi-cloud environment, or in a hybrid combination
- Easy integration across your enterprise data systems and tech stack, from identity providers to cloud permissions systems to infrastructure to apps and data stores, to provide true end-to-end visibility into data access and relationships
- Comprehensive visibility, with a single pane of glass that coordinates the complexity of authorization across multiple systems, and provides actionable insights for intelligently managing and remediating authorization to support corporate standards, compliance mandates, and security concerns
Conclusion
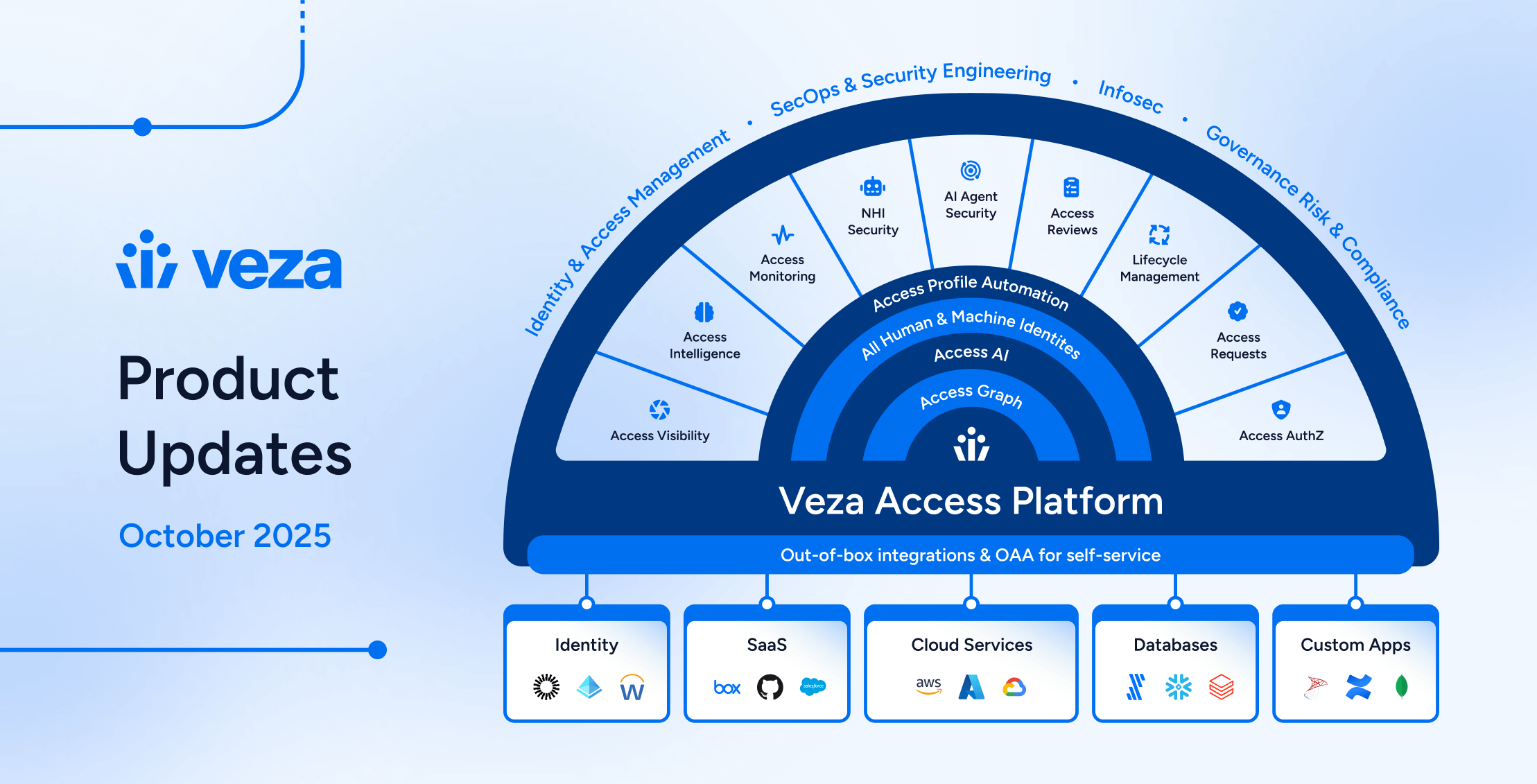
Enterprise data demands the highest level of protection…but it doesn’t always get it. Companies need new tools for strong authorization, so they can provide the always-on data access their workforces need while keeping the enterprise safe from data leaks and security breaches. Veza is the data security platform built on the power of authorization, empowring companies to confidently answer “who can take what action, on what data.” Veza integrates seamlessly with your key enterprise tools – identity providers, cloud IAM, apps, and data systems – to meet any data security use case (data governance, privileged access for data, entitlement management, data access controls etc), for any technology. With Veza in place, you’ll be able to define who can and should take what action on what data, and enforce the fine-grained authorization permissions that keep your enterprise safe from privilege abuse – enabling you to confidently utilize your data to the fullest.