The need to quickly ramp up to support remote work sparked companies around the world to adopt multi-cloud environments at unprecedented levels…a trend that shows no signs of abating. By 2022, 70 percent of companies will be embracing multi-cloud or hybrid technologies and tools, according to McKinsey. And a key driving force in this mass migration to multi-cloud is the promise of securing enterprise data—a company’s most fundamental asset—while making it readily available to authorized parties everywhere.
Every single company in the world will need to make better use of data to compete, from moving data to storing it, querying it, analyzing it, visualizing it and monitoring it.
Bessemer Venture Partners || State of the Cloud 2021
With employees accessing high volumes of enterprise data stored across multiple clouds, managing data security is becoming a daunting challenge. In fact, 47% of companies cite data security as a top inhibitor to their cloud adoption, according to the 2021 HashiCorp State of Cloud Strategy Survey of more than 3,200 technology practitioners and decision makers. Many organizations are still struggling to extend an existing infrastructure-centric security approach. But protecting identities, devices, and a redefined “perimeter” simply isn’t enough. It’s data that threat actors are targeting in the first place—a company’s most fundamental, intrinsic asset—and it’s data that organizations need to secure, directly.
Time for a new approach.
What enterprise teams need now is a platform that centralizes visibility and authorization control. Data is the backbone of multi-cloud systems, and to secure these systems organizations need to be able to answer a fundamental question: Who can, and should, take what action on what data? Only then can they confidently make their enterprise data fully accessible to authorized parties without adding to the risk of security breaches or compliance nightmares.
When considering a solution, here are five critical areas of data security worth thinking about:
Consideration 1: Data discovery, visibility, and classification.
Full visibility is mission-critical, for understanding who has access to what data. Unfortunately, the siloed solutions that today’s typical enterprise has are legacy solutions, primarily built to secure infrastructure and apps, not built for the scale of multi-cloud. As a result, these tools don’t communicate well, hampering the full visibility required to effectively manage modern hybrid or multi-cloud data ecosystems. When your teams’ understanding of who’s accessing what data and why is incomplete, confusing, or cumbersome to discover, it all adds up to increased security risk and increased user friction in completing tasks such as audit/compliance reporting. Solving this once and for all requires a platform-centric approach that surfaces a comprehensive view of all data activity.
Consideration 2: Data access controls.
When authorization to cloud data is scattered across disparate systems, access is either insecure or inefficient or both. Merely monitoring who has access to what data isn’t sufficient: Enterprise teams need an identity-to-data map (including non-human identities, such as service accounts), and comprehensive, real time, granular control over access so they can safely supply, manage and remediate effective permissions on any data source. A platform-centric approach gives teams the centralized tools they need to confidently provide and withdraw access to any and all data sources based on enterprise rules and security protocols.
Consideration 3: Least privileged access to data.
Privileged access to sensitive enterprise data is a commonplace reality that poses an outsize risk: Verizon’s wide-ranging 2021 Data Breach Investigations Report found that the vast majority of data breaches today are “predominantly driven by unapproved or malicious use of legitimate privileges.” An effective multi-cloud security solution must be able to manage privileged access while limiting data breach exposure, reducing privileged-user friction, maintaining customer trust, and keeping the company continuously compliant. Siloed solutions multiply that mission-critical challenge, but a platform data security solution can dramatically simplify it.
Consideration 4: Data governance.
What good is accessible and secure data if the disconnected nature of modern multi-cloud systems and multiple solutions allows it to become outdated or inaccurate? A reliable modern multi-cloud data solution must also include the capability to centrally manage and automate data governance, to ensure that users across the system can trust the accuracy of data. Of course, the level of authorization needed to update important data is just what threat actors are looking for, so keeping data simultaneously updated and secure requires a level of insight beyond simply knowing who can review it. As regional and industry compliance requirements continue to evolve—and regulators become ever more stringent in ensuring companies meet those requirements—a comprehensive understanding of data and access is becoming mission-critical.
Consideration 5: Cloud entitlement reviews.
Entitlement reviews can be time-consuming, but failing to manage entitlement creep can put an organization at serious security and compliance risk—a risk that compounds quickly in a multi-cloud environment. Whether it’s reassigned or promoted employees whose responsibilities have changed or former employees whose legacy access may not be fully disabled, strong governance of entitlements, including entitlements for data stores (data lakes, data warehouses, data lakehouses etc), is essential. And entitlement management becomes incredibly effective when you are able to manage entitlements with full identity context across cloud identity, service accounts, and local users.
And only a centralized platform approach makes it feasible for companies to reliably manage all cloud entitlements risk on an ongoing basis.
Getting to future-proof data security that’s driven by zero-trust and spans multi-cloud environments requires new thinking. And the clock is ticking: Multi-cloud migration is already fully underway, traditional security perimeters are eroding, and attack surfaces are expanding—to the delight of threat actors.
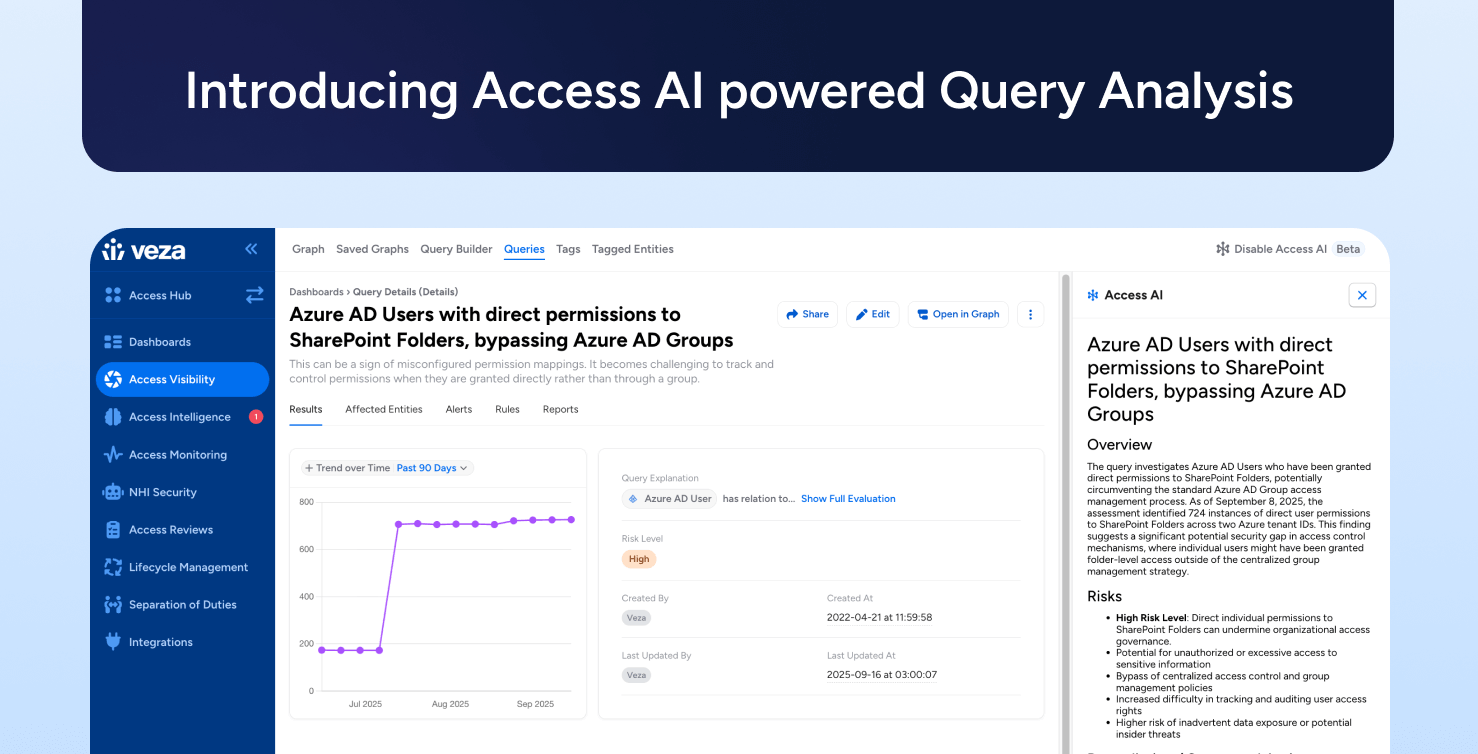
Fortunately, this is the challenge that Veza was born to solve.
We provide enterprises with a robust and comprehensive data security platform built on the power of authorization. With Veza, organizations leverage rich authorization metadata across identity providers, cloud permissions sytems (cloud IAM), apps, and data systems, to address key data security challenges around data governance, privileged access for data, cloud entitlements, and more.
Data security really boils down to one question: Who can and should take what action on what data? Veza puts companies in a position to answer that across their entire ecosystem, by replacing increasingly ineffective siloed solutions with a seamless, centralized data security platform. We help organizations around the world confidently secure their enterprise data, wherever it lives, while keeping it effortlessly accessible to authorized parties.
Why wait any longer? For more on how Veza can help your organization incorporate data security into zero trust initiatives, sign up for your free trial.