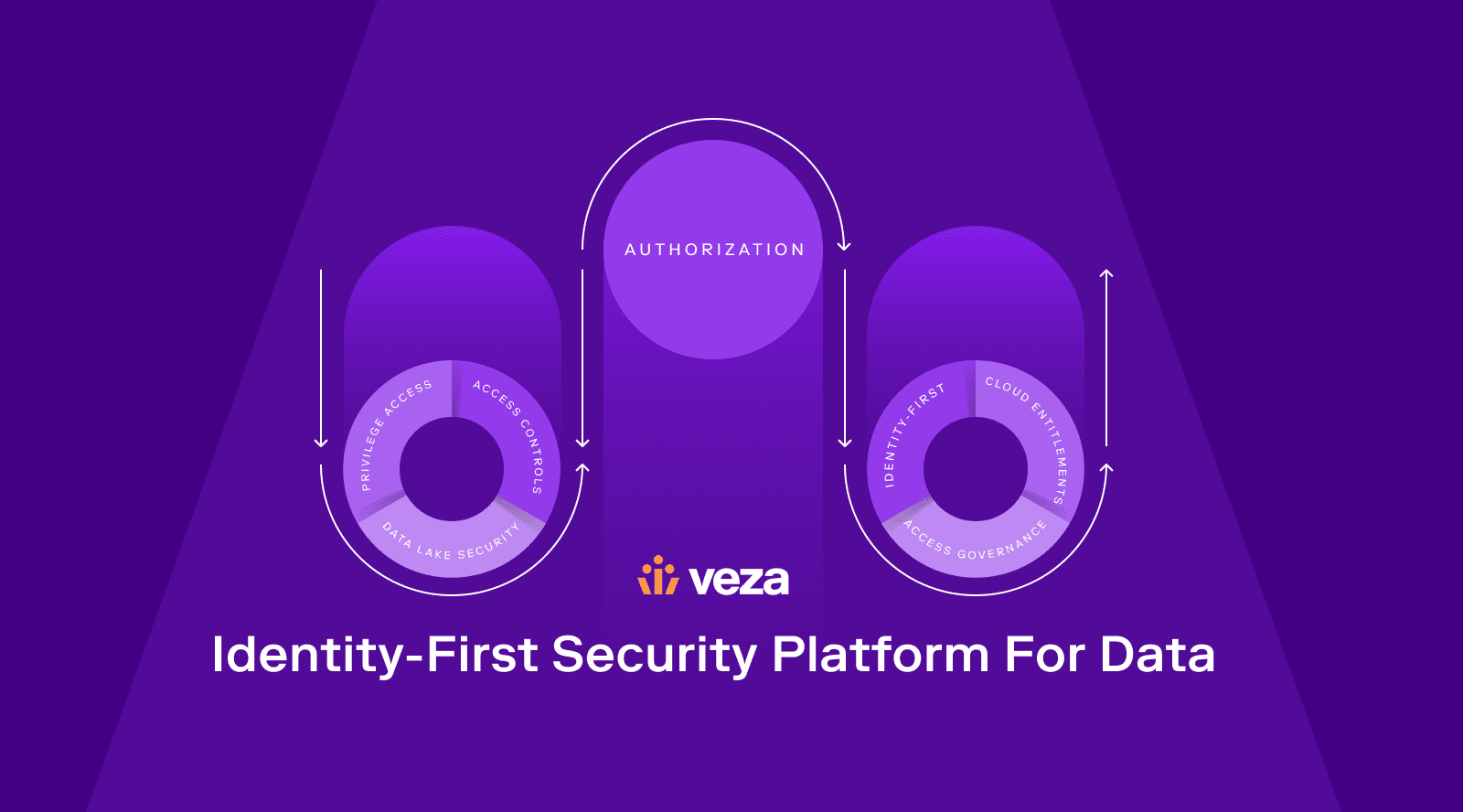
Gartner recently published analysis on security spending that lists critical market segments of data security, identity access management, and cloud security, projected to reach a combined spend of ~$30B in 2023, representing ~20 YoY% growth. Meanwhile, AWS published their security predictions, including organizations moving to “continuous security and compliance” and identifying “managing identities and permissions” as a key frontier.
These market segments are front and center as we build Veza and the projected growth and observations are critical to what we see going into 2023:
New Threats
PREDICTION 1
Russian-led Cyberattacks Target Western Organizations
As Russia experiences setbacks on the battlefield in Ukraine, they’ll do everything they can to create pain for Western Europe in hopes of creating leverage at the negotiating table. Expect to see Russia-originated attacks, as well as the Russian government’s tacit approval of Russian-linked cybercriminal gangs targeting Western organizations. This will include ransomware to generate cash and attacks to disrupt society and infrastructure.
PREDICTION 2
China IP Theft Rises in the United States
New U.S. controls on export of high-end semiconductor production will drive China to increase their attempts at IP theft. Xi’s stated strategic goal of being a long-term leader in AI is directly challenged by this policy, and his government has demonstrated political will to plan and execute on a long-term horizon. The latest policy shift will make IP theft more attractive for China, since acquiring this technology on the open market is effectively impossible. This is already happening, but I predict we’ll see a lot more in 2023.
Trends to Watch
PREDICTION 3
Consolidation in Security
Tough times will mean more M&A in security and identity in 2023. Just this past summer, private equity firm Thoma Bravo completed its acquisition of Sailpoint, KKR completed its acquisition of Barracuda, and CrowdStrike announced plans to buy Reposify. Their investors may appreciate tighter reins on the finances, but it could come at the cost of innovation when acquired companies push for profit and cut R&D. Meanwhile, progressive buyers will find that early-stage security companies, hungry to hit their growth goals, bend over backwards to help their CISO customers succeed. The well-funded startups will also use this year to grow their rosters and expertise in certain areas by acquiring smaller startups.
PREDICTION 4
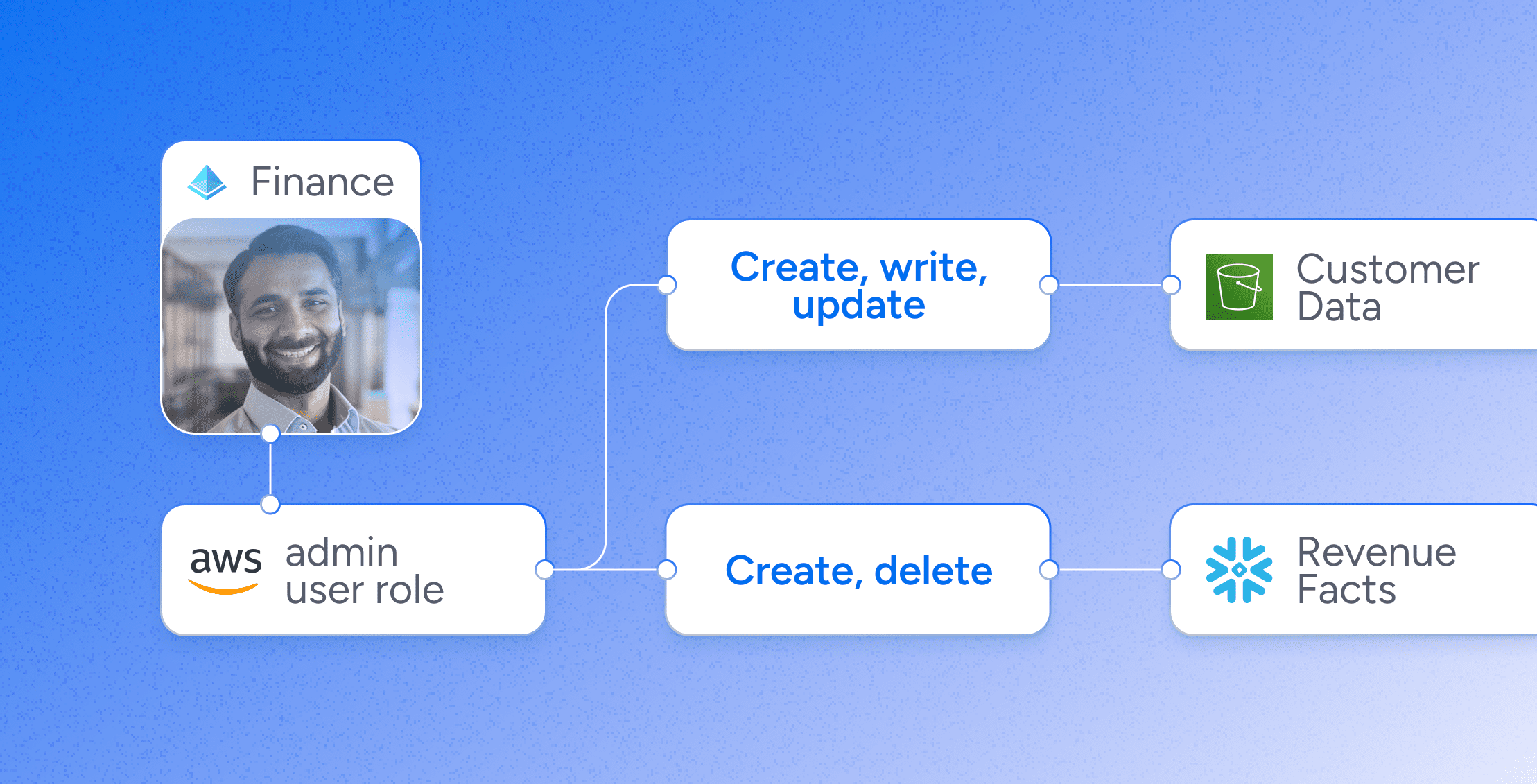
CISOs Tackle Security in The Data Lake
Now that companies recognize the value of data, they are keeping all of it, just in case, and their preferred storage is the data lake. With various analysts and data scientists accessing the data lake for so many purposes, it is harder than ever to configure permissions. Who can take what action on data in the lake? The folks in IT who receive requests for access feel pressure to respond. After hundreds of requests, it’s hard to not start clicking “allow.” The inevitable result is that companies will accrue “access debt.” In 2023, CISOs will start looking for ways to monitor and trim their access debt.
PREDICTION 5
Identity-First Security Takes Off in the Enterprise
Data democratization is here, distributed across a hybrid cloud that includes transactional data systems like Active Directory, Oracle, and SAP. As companies try to map which identities (people) can access which data, they’ll see that the old way of rules and policy-based engines can no longer handle the volume. Enterprises will find it difficult to make real progress on their “least privilege” intentions. In response, security companies will launch new capabilities using AI and ML to prune access on a continuous basis.
PREDICTION 6
A Lingua Franca for Authorization
RBAC (role-based access control), a method of restricting network access based on the roles of individual employees within an organization, has always brought challenges. It’s complex, technical, manual, and unique to every system. Other types of access control, like ABAC (attribute-based access control) add to the complexity. In 2023, identity professionals will turn to Authorization technology as a better way to control who can create, read, update, and delete data. This is especially important for larger organizations with hundreds or thousands of users. Common standards will begin to emerge around a universal model for RBAC.