“I don’t know who has access to my most sensitive data,” he said.
I couldn’t believe it. I was on a call with the head of information security for one of the largest banks in the world — the leader of a massive team of engineers, security specialists and former intelligence officers, all of whom were armed with the most advanced technology available — and he was telling me that if cyber criminals broke into his sprawling hybrid cloud network comprised of thousands of data systems, apps, and cloud services, he would not know what data was at risk.
That phone call two years ago highlighted a gaping hole in data security. It also kicked off a journey that led us here. Today we are announcing the public launch of our new company: Veza, the data security platform that makes it easy to understand, manage, and control who can and should take what action on what data.
New Challenges in the Cloud
Organizations around the world are facing significant challenges related to digital transformation. Data is their most valuable asset and sharing it makes it worth more. We live, work and play remotely and online, creating data exhaust and requiring instant access to data. CIOs predict 44% of workloads will reside in the public cloud by 2024 and the amount of data in the world is expected to triple from 2020 to 2025. Meanwhile, incidents of cyber crime and ransomware are skyrocketing. By 2025, at least 75% of IT organizations will face one or more attacks, according to Gartner, which predicts a seven-fold or higher rate of growth.
The Common “Blind Spot” Across Data Security Solutions: Authorization
Organizations are rushing to the cloud even though they know they’re missing a critical piece of data security: authorization. They have no choice: If they don’t trust employees and partners with their data, their business won’t make it. But no one wants to be a headline. They’re constantly facing the tension: Trust more, or control more?
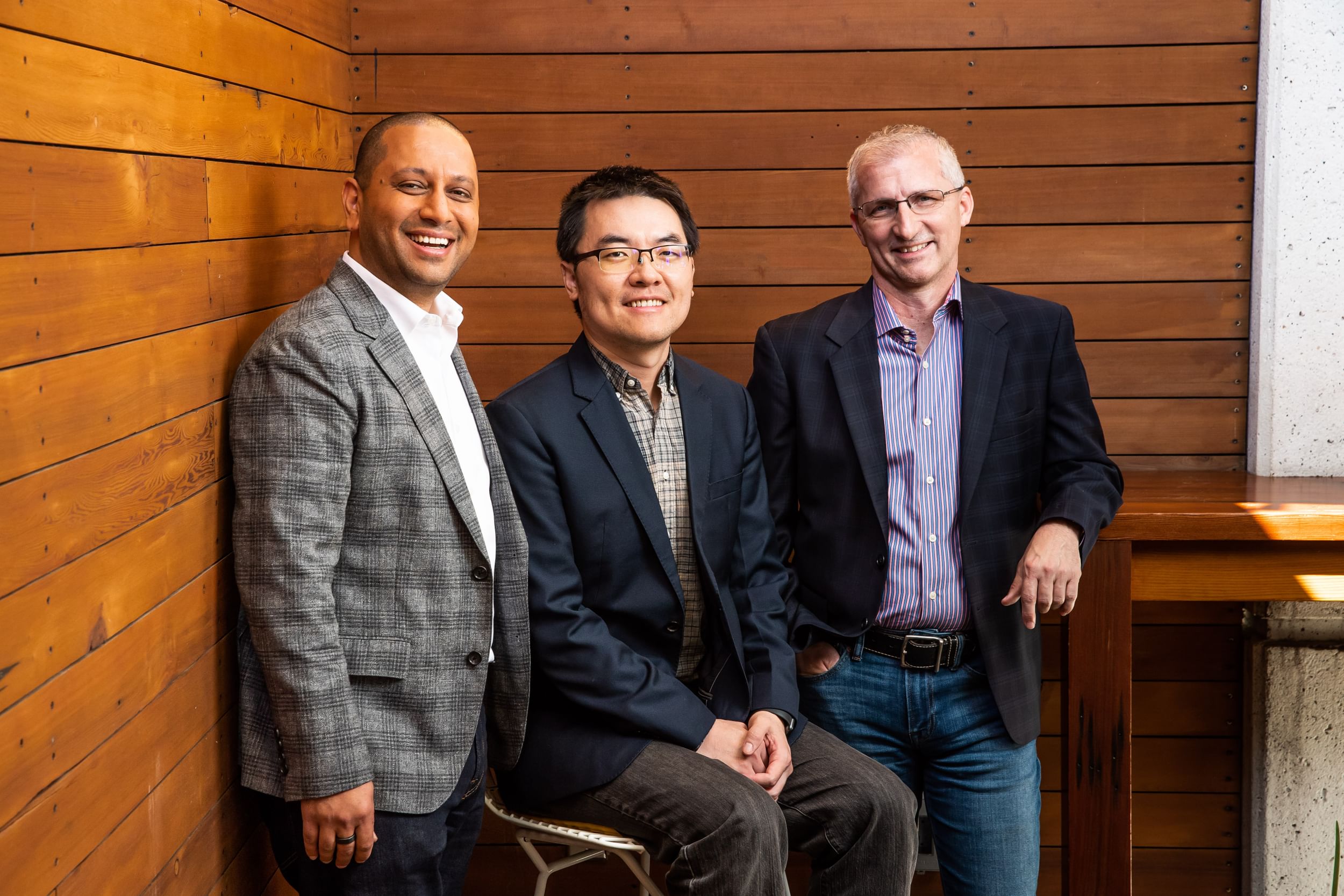
A couple of years ago, my co-founders and I saw an evolutionary event coming — and fast: the world’s data was finally transitioning to the cloud. Having built data systems for the last two decades, we wanted to find and solve the biggest problem we could find related to data. We called on dozens of senior tech contacts and asked them each the same question: “What is your biggest worry related to data in the cloud?” When multiple answers sounded like the quote at the start of this blog post, my co-founders and I made dozens more calls and heard the same sentiment. We were onto something!
When asked to describe “data security,” we heard the same answer from every CTO, CIO, CISO, and more:
- Where is my data?
- Where does this data come from?
- What is the nature of this data?
- Who has access to this data?
- Who is accessing this data?
- Where are the entitlements for data?
- Who has what privilege?
Veza’s Solution: The single source of truth for authorization
As we analyzed the market, we found that existing security products had been built for legacy enterprise systems and barely skimmed the surface of the authorization problem. It became clear that as organizations were moving their data to systems built for the cloud, any authorization solution would need to be purpose-built for those systems. We realized that we had a once in a lifetime opportunity to build a new class of security solution that converged seven silo’d data security use cases.
As engineers and builders ourselves, we believed that in order to build a foundational approach that would meet requirements today and for decades to come, we had to get to the source of truth: the authorization “metadata.” Authorization is system specific and sits in silos — RBAC, ABAC, IAM, ACL, et al — all for apps, data, and services. The solution would need to understand and unify multiple authorizations from the user all the way to the data. This led to our key differentiation: The Authorization Metadata Graph — the fundamental building block that incorporates and unifies heterogeneous authorization dialects, including identities, Cloud IAM (AWS IAM, Azure RBAC, GCP IAM), RBAC (and, PBAC, ABAC, and many more!) of different data systems, apps, and cloud services.
Meet Veza Real-Time Search: Revealing the Truth on Who Has Access to What
Veza is the only data security platform that can show you the truth of your data permissions — or authorization — across your organization’s entire cloud ecosystem. The first time we show people what their data permissions or authorization truth really looks like, they’re floored. One customer did their first Veza search on their head of marketing. What they discovered was terrifying: he had access to the company’s source code and he didn’t even know. Another customer discovered that a large, outsourced customer service organization in another country had access to all of their customers’ emails. If they got phished and those emails got sold on the black market, that would lead to a very public, very expensive breach of trust.
Gaining Control with Veza Violations, Recipes, Rules, and Recommendations
Veza is the only solution that can help you reach and maintain your ideal state of permissions. With Veza, you can search by person, team, or even a specific data object — right down to the column level in a spreadsheet. This search can span and connect IdPs, multiple clouds, and disparate end datasources. Veza is a critical tool for our customers to find, fix and proactively monitor their end-to-end user and data authorization — all via pre-built alerts, violations and recipes that can be integrated with any enterprise tooling such as ServiceNow, Microsoft Teams, JIRA, Slack, etc.
“Zero trust” without authorization management is just security ‘theater’
Many companies do access reviews for compliance and to meet regulations. These are manual, labor-intensive, time consuming processes involving teams across the organization. It’s so invasive that most companies only do this once a year, if at all. If they have a product for these reviews, they almost always stay at the identity layer, which means users, groups, and roles. They don’t let you see what data is involved. The end result is that many of these reviews are woefully incomplete and quickly outdated. You might pass an audit, but it doesn’t increase your level of data security. But with Veza, reviews are granular all the way to the individual data access rights, and are constantly monitored.
Veza’s Mission: Bringing Trust to “Zero Trust”
As a determinedly optimistic person, I find most of the security industry’s marketing to be overly negative and fear-based. “Who’s trying to hack you right now?” and that sort of thing. But I’ve been working in this space for decades and have found that the people in these positions, CISOs and their teams, they’re not fearful. They’re steady. Reliable. Prepared. They’re driven to protect their companies and their customers. What matters most to them is earning and maintaining trust. It’s our responsibility to develop technology that empowers security and data leaders to be strategic — not to instill a sense of powerlessness or fear. That is why our mission at Veza is to help organizations trust confidently so they can unlock the value of their data.
For the past 2+ years, our remote-first team has been operating in stealth in order to create an unshakable foundation for an enduring business. We are customer-obsessed and have earned the trust of some of the most discerning organizations in the world, including ASAPP, Barracuda Networks, Choice Hotels, InComm, The Translational Genomics Research (Tgen), and many more across Fortune 500/1000 and emerging organizations. Our team is committed to level-5 leadership — an operating mode that requires an uncommon combination of staunch will and humility. If this post speaks to you, we would love to hear from you:
*If you want to integrate your apps to Veza, please visit our GitHub community page.
*If you want to see our product in action, you can reach out to us here.
*We’re hiring! If you would like to join our team, please visit our open positions.